40+ WordPress Hacking Statistics (Patchstack 2026 Data)
Last updated: March 2026
11,334 vulnerabilities in a single year. 91% in plugins. Exploits launching within 5 hours. Here are 40+ WordPress security and hacking statistics from Patchstack’s 2026 report — the data every WordPress site owner needs to see.
Key WordPress Security Statistics (2026)
- 11,334 vulnerabilities discovered in 2025 — up 42% YoY (Patchstack)
- 91% of vulnerabilities are in plugins; only 6 in WordPress core
- Median time to mass exploitation: 5 hours
- 46% unpatched at time of disclosure
- 43% exploitable without authentication
- Traditional WAFs block only 12% of WordPress-specific attacks
WordPress Vulnerability Trends
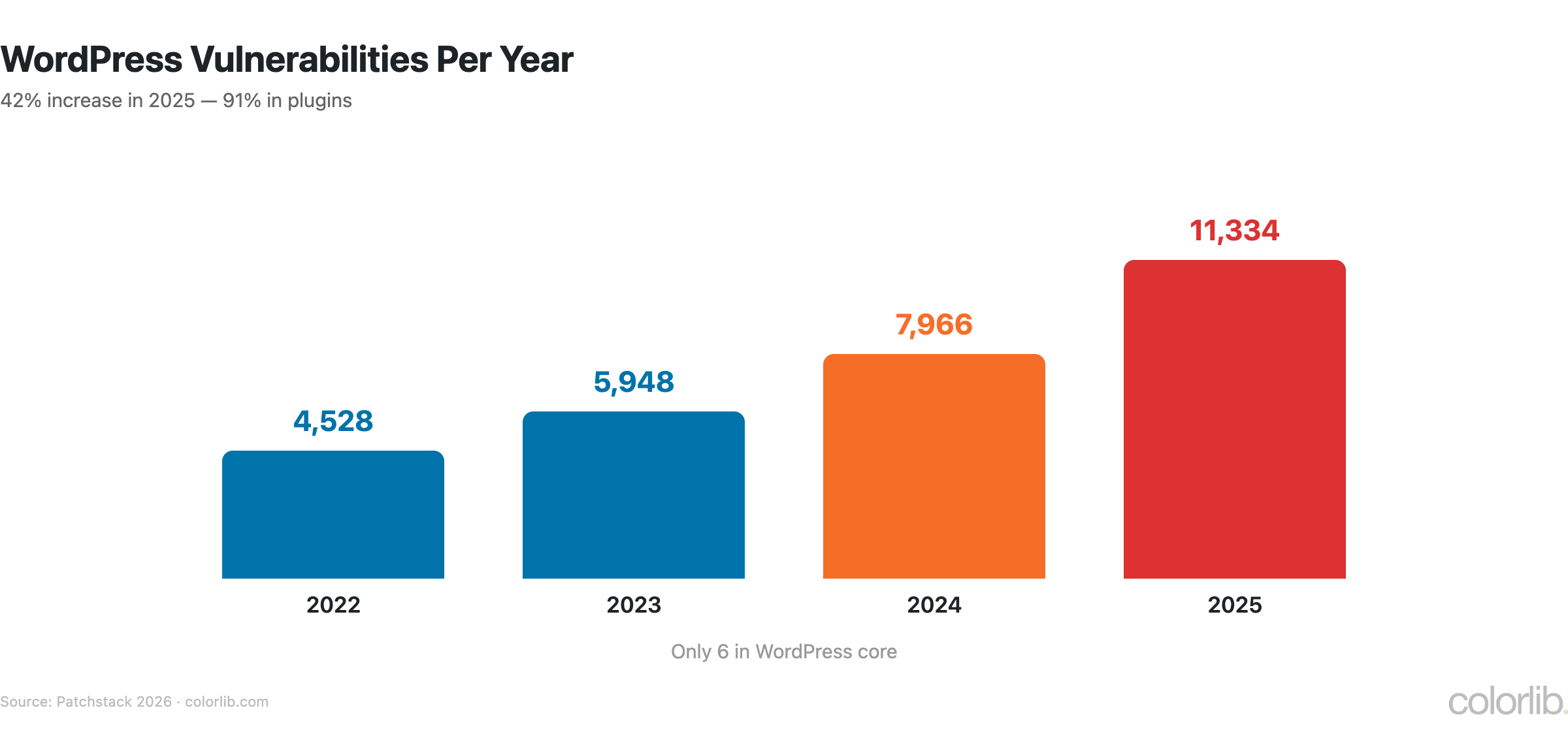
| Year | Vulnerabilities | YoY Change |
|---|---|---|
| 2022 | 4,528 | — |
| 2023 | 5,948 | +31% |
| 2024 | 7,966 | +34% |
| 2025 | 11,334 | +42% |
- Cumulative known vulnerabilities: 64,782
- 333 new vulnerabilities in a single week of January 2026 (36/day)
- Highly exploitable vulnerabilities increased 113% YoY in 2025
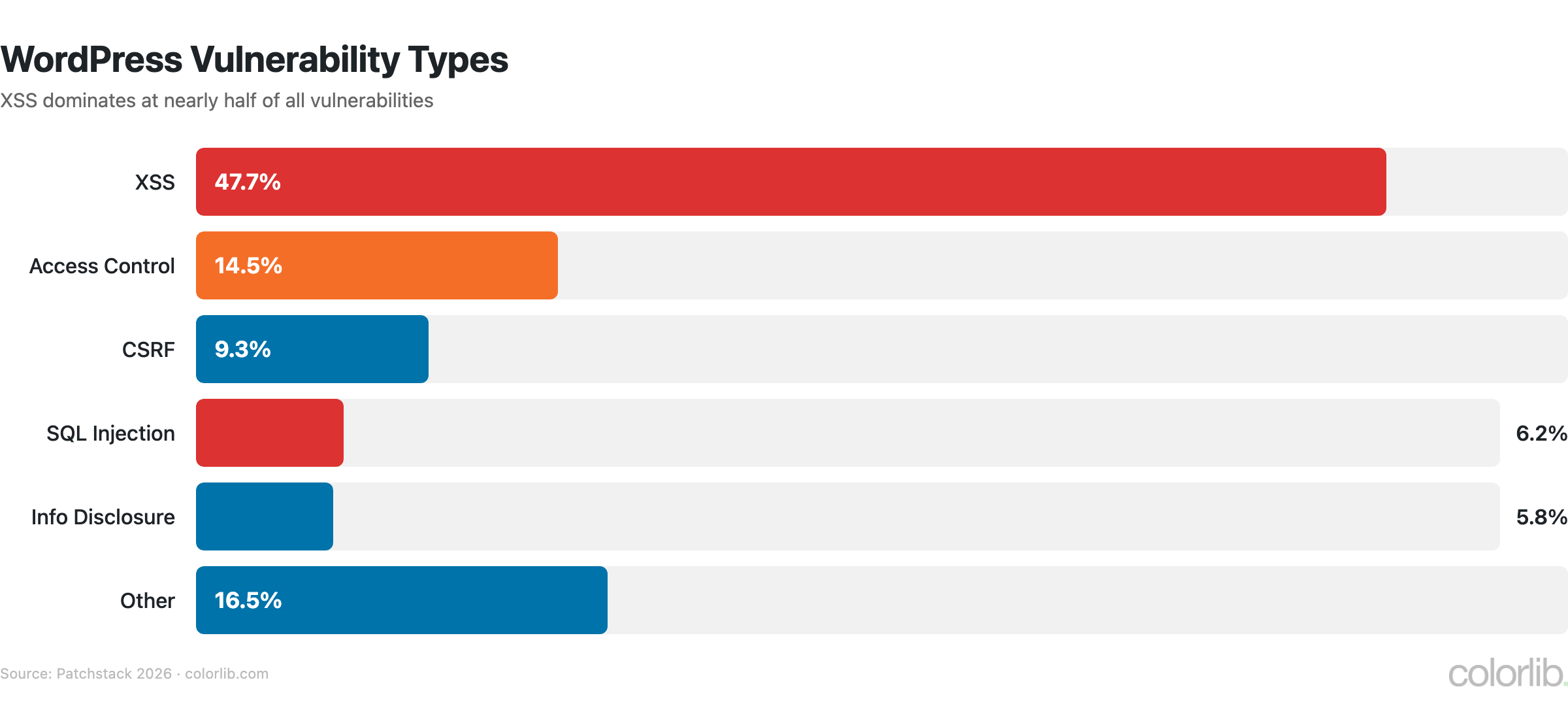
Vulnerability Breakdown
| Category | Percentage | Count (2025) |
|---|---|---|
| Plugins | 91% | ~10,314 |
| Themes | 9% | ~1,020 |
| WordPress core | <0.1% | Only 6 |
| Vulnerability Type | % of Total |
|---|---|
| XSS (Cross-Site Scripting) | 47.7% |
| Access Control | 14.5% |
| CSRF | 9.3% |
| SQL Injection | 6.2% |
| Information Disclosure | 5.8% |
| Other | 16.5% |
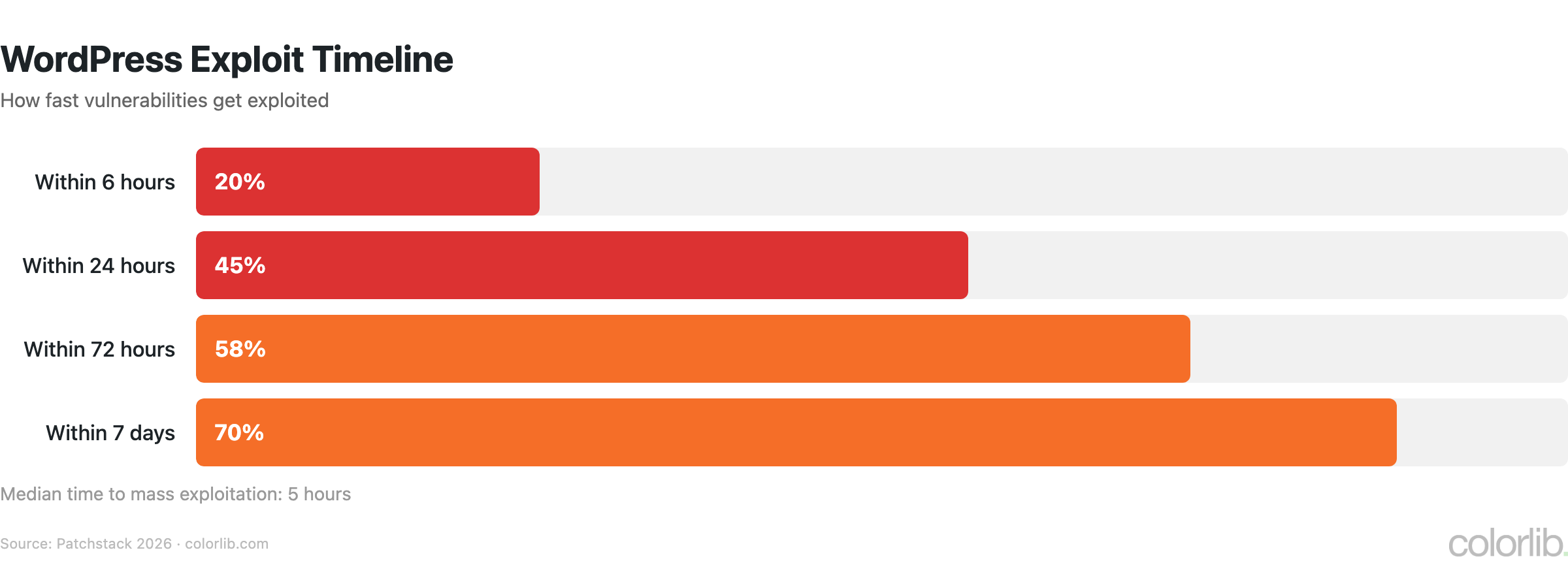
Exploit Timeline
| Timeframe | % Exploited |
|---|---|
| Within 5 hours (median) | Mass exploitation begins |
| Within 6 hours | 20% |
| Within 24 hours | 45% |
| Within 72 hours | 58% |
| Within 7 days | 70% |
Critical insight: 46% of vulnerabilities had NO developer patch when disclosed. You can’t rely solely on updates — you need proactive security (WAF, monitoring, minimal plugins).
WordPress Security Practices
- Traditional WAFs block only 12% of WordPress-specific attacks
- 43% of vulnerabilities are exploitable without authentication
- 45% of AI-generated code contains security flaws
- ~2.5% of WordPress sites run version 4.x or older — severe security risk
- Only ~48% run a PHP version with active security patches
Key Takeaways
- WordPress core is secure. Only 6 vulnerabilities in 2025. The problem is plugins (91%).
- Speed matters. Exploits launch within 5 hours. Automated updates are essential.
- Less is more. Every plugin is an attack surface. Remove what you don’t use.
- WAFs aren’t enough. Traditional WAFs block only 12%. Use WordPress-specific security.
Sources
Frequently Asked Questions
How many WordPress sites get hacked?
With 11,334 vulnerabilities discovered in 2025 and exploits launching within 5 hours of disclosure, thousands of WordPress sites are compromised daily. The exact number isn’t tracked globally, but 30,000 websites of all types are hacked every day.
Is WordPress secure?
WordPress core is very secure — only 6 vulnerabilities in 2025. The risk comes from plugins (91% of vulnerabilities) and outdated installations. A WordPress site with minimal, updated plugins and proper security is as safe as any platform.
What causes most WordPress hacks?
Vulnerable plugins cause 91% of WordPress security issues. XSS (cross-site scripting) accounts for 47.7% of all vulnerabilities. 43% can be exploited without any authentication.
For broader cybersecurity data, see our Hacking Statistics and Password Statistics. For WordPress help, browse our WordPress Statistics.






Hi! I’m looking into having a website built for my business and all of the companies I’ve spoken to, except one, have said WordPress is the way to go for best SEO. The one company advising against WordPress sent me this article and said WordPress makes businesses too vulnerable so they don’t create on WordPress. In your opinion, which platform is best for SEO for a small service based company that doesn’t sell products online. Ty!
Renee,
WordPress is as safe as a popular CMS can be. Yes, many WordPress websites go get hacked but that’s because 810 million websites use it, so even a tiny percentage of websites means that millions of website get hacked.
However, we have too look into main reasons why WordPress websites get hacked and the main one is that people use user name “admin” and a simple password reused on many other websites and other online accounts. Just changing a user name to anything other than “admin” will protect your website fro majority of attacks.
Another of top reasons is using an outdated version of WordPress core, plugins and themes. Updating these things takes seconds and can be automated so WordPress does all the updates for you. With these simple things out of the way, there is slim to no chance that your website will ever get hacked.
Of course, make sure to have at least a daily backups (automated), so if ever happens you can fix everything within few hours. Here are the best WordPress backup solutions that you can use or just use a WordPress hosting that offers backups as part of their service.